Different types of malware
- Unwanted advertising in the browser

- Call to downloading shareware and freeware
- Disguises itself as a standard program but has malware embedded in the background
- Annoying advertising while surfing on internet
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.- Observes the system and network
- Monitors activities as well as conversations by using the microphone and camera from the user

- Sends user data to third parties and hackers
- Uses data to produce user specific advertisement
Most interesting data:
- Registration data
- Credit card numbers, financial details
- Secret conversations
- Browsing history
- Search history
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
- A virus attaches itself to a program or file
- Requires action from the user
→ It waits passively to be spread onto a new system - Virus copies itself while program is running
- Virus infects other programs with malicious code
- Programs infect other standard programs on the computer (snowball system)
- Changes, damages or destroys personal data
- Damages hardware
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
- Programs that make countless copies of themselves
- Similar to a virus but they can be transmitted without a person's action

- Spread through networks and gaps of operating systems
- Stay active in infected devices
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.- Acts like a reputable program
- Performs another function in the background unnoticed
- By executing the program, attackers get access rights to the system and personal data
- Attackers install more malware, execute programs or publish personal data
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
- Revokes access rights

- Blocks important files
- Demands ransom to get back access rights (usually in bitcoins)
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.- Method to steal the user’s identification and passwords illegally trough fake SMS and mails
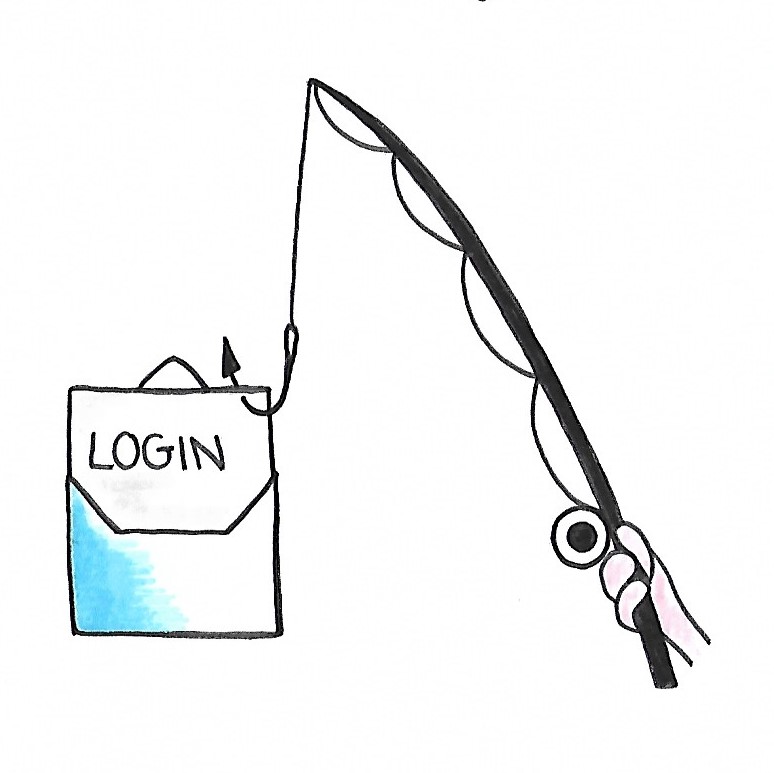
- Attackers “fish” for access data
- Usage of a professional form (E-mails from the bank)
- Focus is on data for online banking , online shops and social networks
- Attackers receive a new identity (the identity of the user)
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
How to identify phishing mails?
- Grammar and spelling mistakes
- Use of foreign language (English or French)
- No personal approach but “Dear customer”
- Urgent need for action (especially in a short term)
- Call for personal and secret information
- Request to open an unknown attachment
- Suspect links which need to be opened
- Unknown addressor
In most cases, banks are affected. Therfore, attention needs to be payed to the banks name and the responsible bank advisor.
Example:
- Access method from the “backdoor”
- Software with security gaps
→ Could be installed by a manufacturer
consciously or a malware secretly
Allows external users to access the system remotely…
- Through gaps
- By avoiding a security mechanism (like a login)
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
- DOS = Denial of Service (one attacker)
- DDOS = Distributed Denial of Service (more attackers or infected computers)
- Attackers make servers or services
unavailable
→ Overloading the system by sending multiple requests
→ Exceeding the website’s capacity
→ Crashing the website
- Requests are much slower or ignored
- Main aim: Preventing users from accessing the target page
- Known victims are Amazon and eBay
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
- Distributed computing network (technical view)
- Network of computers that execute
malware automatically
- Attackers access to the computers remotely
- Botnets only work while the computer is running and part in a network
- In most cases botnets are used for criminal activities…
- Act like distributed centers to send fake e-mails (Phishing)
- Provide remote access to foreign systems so that personal information can be sold (ex. In the Darknet)
- Get a lot of memory storage for destructive data files
- Build connection to other computers to hide the origin address
 This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
This work is licensed under a Creative Commons Attribution-ShareAlike 2.0 Generic License.
How do botnets work?
- Users with an undamaged but unprotected system call to infected website
- On this manipulated website they catch malware
- The infected computers (called “Bots” now) become part of a network of more controlled computers
- After that, these computers receive commands from hackers (botmasters)
- They do communicate with each other but work independently
- Bots obey the tasks from the hacker
